Threats Without Borders - Issue 248
Cybercrime Investigation Newsletter, week ending August 17, 2025
I’m old, so the ads I see while watching TV mainly include products like arthritis relief, foot supports, and the necessity of purchasing gold. One commercial I've seen repeatedly over the past few weeks promotes a company that offers protection against home title fraud, aka deed theft.
It’s a frightening ad featuring a girl sitting in a car ranting into a camera who describes how these terrible events occur and will leave you homeless. The ad is fast-paced and striking, with blinking bold font and a narrator with a deep, commanding voice. I’m sure it’s extremely effective in converting its targeted audience – low-tech older adults who are terrified of losing their homes.
And it’s one of the most common questions I receive when speaking with older adults. Is home title fraud real? Can someone truly steal my home while I’m living in it without my knowledge?
And I have to answer, I honestly don’t know.
Seriously, I understand the attack flow they offer, but it seems like one of those possible versus plausible conflicts. Is it possible? Yes. Is it plausible? Probably not.
And even if attackers manage to change the title into the control of an identity they own, what next? How do they monetize it? They might be able to sell an abandoned or unoccupied property easily, but how do you sell a home that is actively inhabited without the residents noticing? Think about all the steps involved in selling a home, and the remoteness that no one along the way will likely realize someone is already living there, unaware of this manipulation.
And it seems that in today’s digital age of record-keeping, it would be easy to correct. The aggrieved homeowner should be able to easily demonstrate they weren’t involved in the corrupt title transfer.
I think this would be a lot of work for the bad guys with a low probability of payoff. They could invest their time into many other high-profit and highly successful frauds, so why involve themselves in something as highly regulated as residential properties?
However, upon researching the issue, I find no shortage of anecdotal stories from those who allegedly know someone who this crime has victimized. It appears that every Redditor has a second aunt or neighbor “down the street” who has had their home stolen out from under them.
So, I come to you. Have any of you ever actually investigated a case of home title fraud where someone's property deed was transferred out of their name without their knowledge?
Comment below or send me an email: matt [@] threatswithoutborders.com
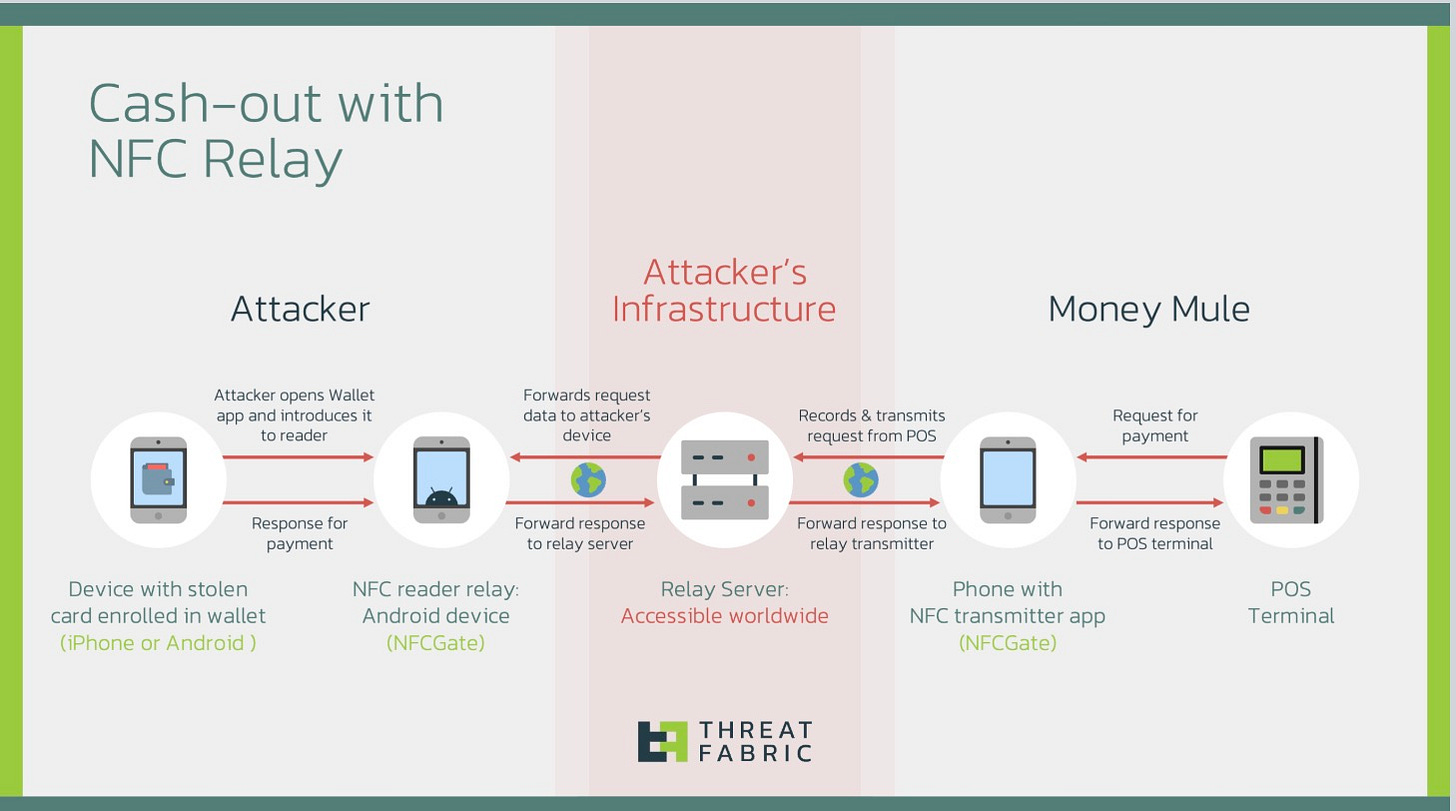
Recorded Future provides an in-depth analysis of the "ghost-tapping" attack vector, a relatively new technique primarily employed by Chinese-speaking threat actors to commit retail fraud. Ghost-tapping involves using Near Field Communication (NFC) relay tactics to link stolen payment card details to mobile payment services, such as Apple Pay and Google Pay, allowing mules to make in-person purchases of physical goods at retail stores.
The report outlines the key elements of ghost-tapping campaigns, which necessitate collaboration between cybercriminals and established Chinese-speaking criminal syndicates. Cybercriminals use phishing, malware, and social engineering to obtain payment card credentials and link them to mobile wallets on burner phones, which they then sell to the syndicates. The syndicates then hire mules, often foreign nationals posing as tourists to make purchases using the compromised payment cards.
The bulk of the research is from Threat Fabric.
I suggest you read both reports since the attack will soon be on our shores, if not already.
https://www.recordedfuture.com/research/ghost-tapping-chinese-criminal-ecosystem
https://www.threatfabric.com/blogs/ghost-tap-new-cash-out-tactic-with-nfc-relay
The News…
Coming from government, specifically law enforcement, I feel like I should write more about the growing threat of cybercriminals selling active government and police email accounts on the dark web. Police departments provide very little awareness training, and employees are regularly falling for social engineering attacks, resulting in compromised accounts. These compromised accounts are used to impersonate officials, send fraudulent legal requests, and access sensitive law enforcement systems, with threat actors marketing them as commodities offering various capabilities. Abnormal Security does a great job detailing the issue. https://abnormal.ai/blog/compromised-police-government-email-accounts
Great! Now we have luggage fraud! Travelers are being warned about a popular scam at airports where scammers are using discarded baggage tags to make false claims to airlines and steal personal information. The tags, which contain barcodes with sensitive information, can be used by scammers to identify travelers and file false claims for missing items. Airlines are advising passengers to remove their baggage tags immediately after collecting their luggage and dispose of them securely. https://www.the-sun.com/travel/14957685/delta-employee-warns-travelers-scam-baggage-tag-personal-information/
The popularity of Capture The Flag-style challenges, such as Hack The Box, TryHackMe, and Overthewire, shows that there is a large number of “hackers” out there. Unfortunately, there aren't enough legitimate “penetration testing” jobs for all of them, so some put on the black hat. And the Medusalocker ransomware gang is there to welcome aspiring pen testers with open arms. https://www.fortra.com/blog/medusalocker-ransomware-gang-hiring-penetration-testers
Proton has an ulterior motive in writing this, but makes a valid point. Why is Perplexity willing to pay $34 billion—money it doesn’t even have yet—to buy Chrome? Maybe because this would allow Perplexity to collect and monetize user behavior, potentially using it to train AI models and display targeted ads. The acquisition would also give Perplexity a significant edge in the AI search market, as Chrome is a leading browser with a large user base. They also highlight the growing trend of AI companies prioritizing data collection and surveillance-based monetization over user privacy. https://proton.me/blog/ai-browsers-perplexity-chrome-privacy
Three individuals were arrested for the $2 million armored truck heist in Philadelphia, and guess what—a Brinks employee was involved. Watch your people! Excellent work by the FBI and Philly PD! Kudos. https://6abc.com/post/3-arrested-stealing-more-2m-brinks-armored-truck-robbery-outside-home-depot-philadelphias-port-richmond-section/17523900/
Law enforcement in Myrtle Beach, SC has identified 800 victims of a massive check fraud but has only been able to make contact with 100. https://www.wmbfnews.com/2025/08/15/i-feel-violated-myrtle-beach-police-have-contacted-100-victims-2m-check-fraud-case/
The Pennsylvania Attorney General’s Office is still recovering from an attack on its systems, which affected its website, email, and phone lines. Initial reports indicate that the attackers exploited the Citrix Bleed 2 vulnerability, which targeted insecure Citrix NetScaler devices. What a shame. This is a Commonwealth of Pennsylvania IT problem, not an AG’s office issue, but the office is feeling the impact and humiliation of the attack. https://therecord.media/pennsylvania-attorney-general-office-cyberattack
Someone is claiming to have over 15.8 million PayPal credentials with login and password in plain text. https://hackread.com/threat-actor-selling-plain-text-paypal-credentials/
The US Treasury Department proposes adding identity verification to decentralized finance (DeFi) platforms to fight financial crime. This effort aims to prevent money laundering and illegal activities in crypto markets. The plan, rooted in the GENIUS Act, would require DeFi platforms to verify users' identities before transactions, implementing KYC and AML safeguards directly into blockchain systems. Public comments on the proposal can be submitted until October 17, 2025. https://www.federalregister.gov/documents/2025/08/18/2025-15697/request-for-comment-on-innovative-methods-to-detect-illicit-activity-involving-digital-assets
Cool Job
Director of Protective Intelligence, Major League Baseball. https://www.mlb.com/careers/opportunities?gh_jid=7141755
Cool Tool
Find specific files posted to publicly accessible web servers. https://filepursuit.com/
Irrelevant
As the father of two college students, this is terrifying; Entry-level jobs are disappearing at a shocking rate due to AI. https://www.finalroundai.com/blog/entry-level-jobs-disappearing-fast-because-of-ai
Sign Off
I like football, but in October, not August. I just can’t get into it when it’s sunny and 80 degrees. It feels like cheating on summer to stay inside watching TV when the weather outside is so nice.
Don’t give up on summer!
Matt
“FREE” USUALLY MEANS “COSTS SOMETHING OTHER THAN MONEY.”
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.