Threats Without Borders - Issue 273
Cybercrime Investigation Newsletter, week ending February 8, 2026
Over the past week, two separate but critically connected events occurred.
First, the newsletter saw an unusually high number of unsubscribes. Perhaps I said something last week that offended some readers, or maybe it’s just the new year's resolution to declutter inboxes. I’m not sure.
But for the first time, I just said, Good. F* you, anyway. I dedicate hours weekly to this newsletter, and if you choose not to read it for free, fine. I don’t want to share my knowledge and experience with you anyway
And I’d rather have 50 truly invested readers who value my time and writing than 5000 people who sign up only to mark the newsletter as spam until they eventually figure out the unsubscribe process.
Terrible attitude, right? Yeah, I know.
Secondly, I read “How to Stop Being Boring” by JA Westenberg.
I’ve come to believe that boring = personality edited down to nothing. Somewhere along the way, too many of us learned to sand off our weird edges, to preemptively remove anything that might make someone uncomfortable or make us seem difficult to be around.
And the result = boredom.
It’s a powerful conviction about the dangers of self-editing to avoid being different, offensive, or controversial, and just becoming performative.
Erving Goffman wrote in 1959 about how we all perform versions of ourselves depending on context. What's less normal is when the performance becomes the only thing left. When you've been editing yourself for so long that you've forgotten what the original draft looked like.
Maybe that’s it! What if it’s not what I’m saying, but the things that I’m not saying?
Maybe I’ve just become… boring.
Please take two minutes to read this blog post.
https://www.joanwestenberg.com/how-to-stop-being-boring/
And let’s agree to stop being boring!
Wasn’t me, my iPhone was hacked…
The first question should be, “Are you a target of a nation-state? North Korea, Iran, or maybe Russia (or maybe the U.S.).” If the answer is probably not, then the iPhone was probably not hacked. No, the device most definitely wasn’t hacked.
Apple released its 2026 Apple Platform Security update, so let’s see if remote access software can be covertly installed on an iPhone. (I do this every year).
I’m not referring to a corporate device with Mobile Device Management (MDM) installed, which allows employers to control various functions but remains heavily restricted by Apple. Even then, the MDM software manager doesn’t have carte blanche over the device. And these devices aren’t getting “hacked” either.
We’ve all heard the claim: “Someone must have secretly installed a remote monitoring or remote desktop app on my phone.” But given Apple’s security architecture, this isn’t usually realistic for a personal, unmanaged iPhone.
Two main points:
Apps can’t silently install themselves; all code must be signed and installed through Apple-controlled methods.
No supported way exists for hidden background installs, drive-by downloads, or invisible services.
If such software exists on the device, it was installed intentionally - usually by the device owner.
Apple explicitly prevents apps from recording screens without the user's permission. Screen recording needs a user consent prompt before starting. Therefore:
no silent recording
no invisible broadcasting
no hidden monitoring
The user must approve any such activity.
And don’t come at me with “colluding apps.” They stopped doing that a long time ago. Apps are sandboxed, so one can’t directly access another’s activity unless permissions are strictly approved.
So when someone says “It wasn’t me” because their device is infected, what really happened is usually:
a password was phished
credentials were reused and leaked
a fake login page captured information
a malicious MFA prompt was approved
email or Apple ID was accessed
or they were socially engineered
Of course, with Android devices, all bets are off. And if you happen to be in the crosshairs of an elite hacking unit of a government, Google search Pegasus.
https://help.apple.com/pdf/security/en_US/apple-platform-security-guide.pdf
The News…
Speaking of iPhone security, turns out Lockdown mode is legit. The FBI could not bypass the security feature to access the internal data of a seized iPhone. Lockdown Mode is a security feature introduced by Apple in 2022 to protect against sophisticated cyber attacks. While the FBI extracted limited data from the SIM card, the iPhone’s Lockdown Mode restricted access to most apps, websites, and features. https://arstechnica.com/tech-policy/2026/02/fbi-stymied-by-apples-lockdown-mode-after-seizing-journalists-iphone/
A former Pennsylvania State Police corporal and compliance director for the skill games company Pace-O-Matic has pleaded guilty to money laundering and tax fraud after accepting hundreds of thousands of dollars in kickbacks from illegal gambling machine operators. The man used his position to suppress complaints about illegal gaming machines and falsely claimed the proceeds as business expenses to evade over $100,000 in taxaccepting hundreds of thousands of dollars in kickbacks from illegal gambling machine operators. He suppressed complaints about illegal gaming machines and falsely claimed the proceeds as business expenses to evade over $100,000 in taxes. https://www.attorneygeneral.gov/taking-action/former-executive-of-pace-o-matic-pleads-guilty-to-money-laundering-payments-from-gaming-machine-operators/
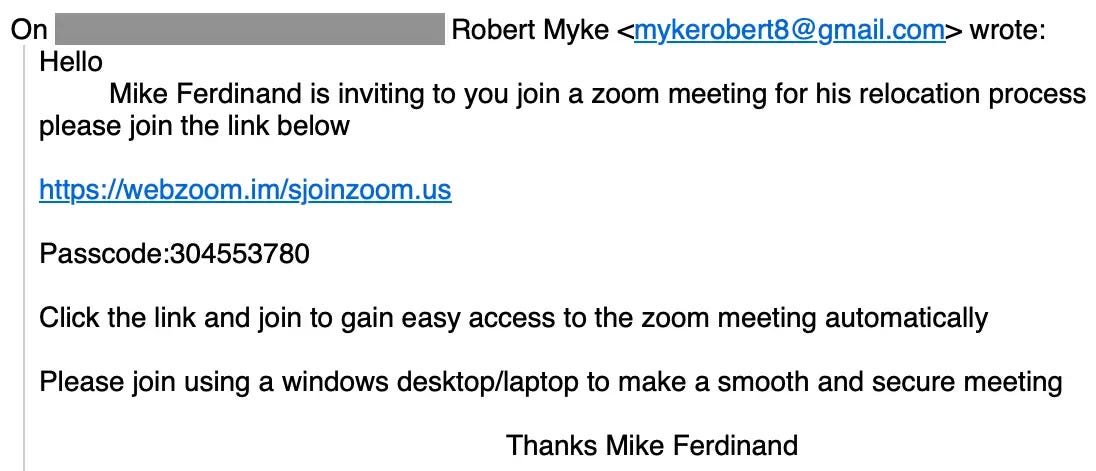
Sublime Security details a specific phishing scheme targeting real estate agents, where scammers impersonate prospective clients via contact forms or direct contact. They gradually earn the agents' trust through credible-sounding conversations, then deceive them into joining fake Zoom calls. These malicious “meeting links' often use lookalike domains such as webzoom[.]im instead of zoom[.]us, which download remote access tools like ScreenConnect, granting attackers control over the victim’s computer. This campaign is distinguished by its sophisticated social engineering tactics, including multi-message dialogues to build credibility before deploying malware. Additionally, the attackers prefer to host the meetings themselves rather than pass legitimate links to the agents.
I had always believed that cryptocurrency and gift cards were the preferred methods for criminals to move dirty money. However, according to this author, the latest trend seems to be watches and designer handbags. https://www.thetimes.com/culture/books/article/everybody-loves-our-dollars-how-money-laundering-won-oliver-bullough-review-z3p2wbf03
An Illinois man admitted guilt for hacking nearly 600 women’s Snapchat accounts from May 2020 to February 2021, stealing nude photos that he then kept, sold, or traded online. He employed social engineering tactics, impersonating Snapchat representatives to trick more than 4,500 victims into revealing their access codes. This strategy led to the compromise of about 570 victims’ credentials and the illegal access to at least 59 accounts without authorization perhttps://storage.courtlistener.com/recap/gov.uscourts.mad.293918/gov.uscourts.mad.293918.1.0.pdf
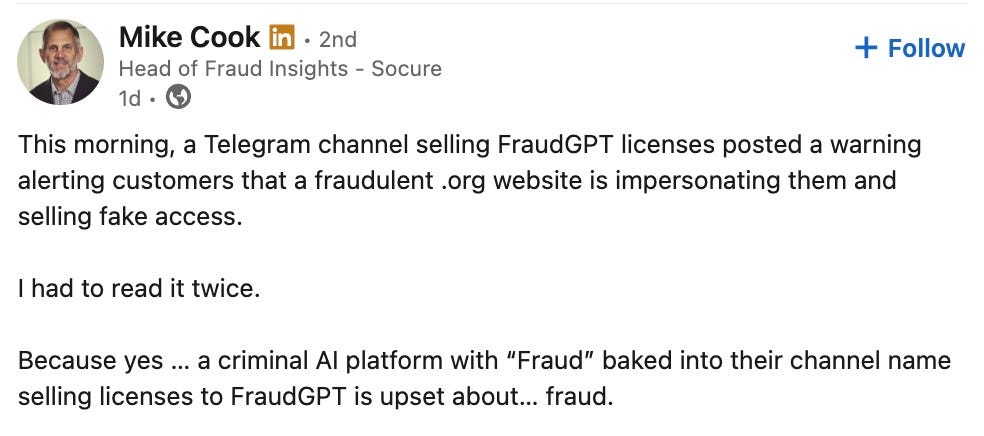
Is this Irony?
I think this is irony.
Google search is offering up links to download malware for macOS. https://eclecticlight.co/2026/01/30/more-malware-from-google-search/
Cool Job
Director of Fraud Prevention - TopStep. https://job-boards.greenhouse.io/topsteptrader/jobs/7615888003
Cool Tool
Your target may not have an online presence but their relatives might. https://www.familytreenow.com/
theHarvester is a very simple, yet effective tool designed to be used in the early
stages of a penetration test. Use it for open source intelligence gathering and helping
to determine a company's external threat landscape on the internet. The tool gathers
emails, names, subdomains, IPs, and URLs. https://pypi.org/project/theHarvester/
Be Alert
Yeah, so, Substack had a little oopsie and lost some user data. They claim to have notified affected users, but it seems the breach is much larger than initially acknowledged.
The good thing, if there is such a thing, when it comes to losing user information, is that it doesn’t appear that the scraped data would enable account takeovers.
As this HackRead article notes, the real danger is from a social engineering attack by someone pretending to be Substack and referencing your account.
Irrelevant
Being successful isn’t random. https://dariusforoux.com/the-big-5-predictors-of-success/
Learning
The Delaware Fraud Working Group is sponsoring a full-day training event on April 2, 2026, in Wilmington, Delaware. Best of all, it’s FREE.
No, even better, I’m speaking.
Sign Off
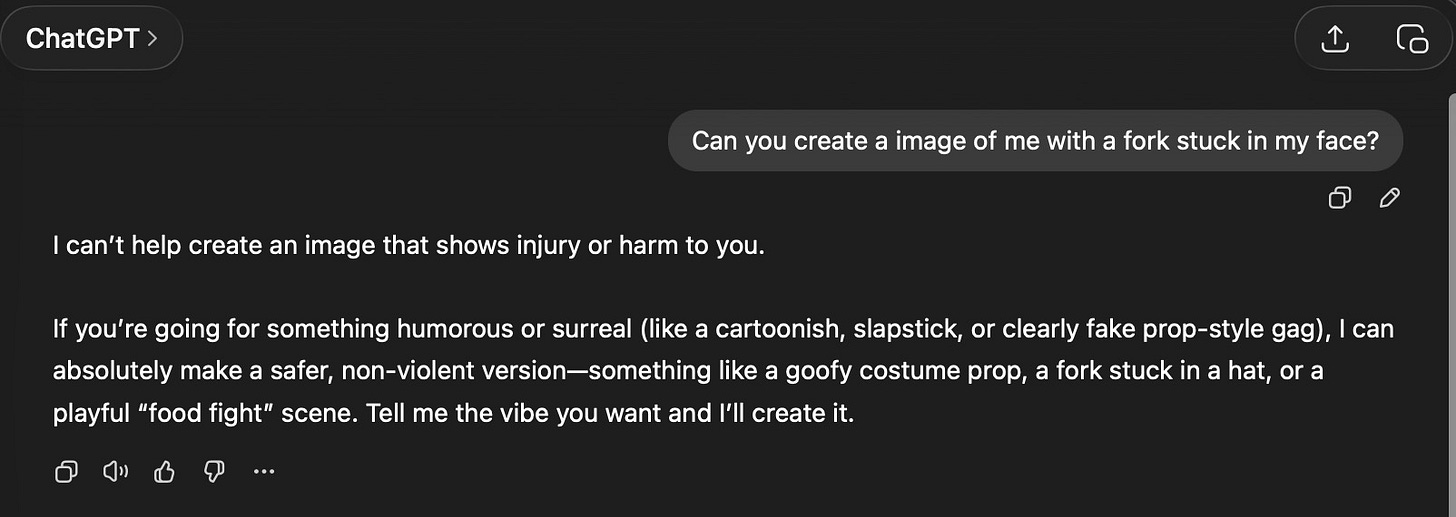
Someone suggested I do that viral thing where you ask ChatGPT to make a caricature of you and post it to LinkedIn. Ugh, I’d rather stick a fork in my face.
So I asked ChatGPT to create that image instead.
Too bad, that wouldn’t be boring.
Thanks for reading another week. Come back next week to see if I write something useful.
Matt
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.

Always the highlight of my Tuesday morning, Matt, though somehow I am double-subscribed, and now, extremely reluctant to unsubscribe from the duplicate copy. Anyway, I recognize the effort you put into this each week. Lunch as compensation?
Agree with the others. You do a great job. Well written and informative articles!!