Threats Without Borders - Issue 276
Cybersecurity Investigation Newsletter, Week ending March 1, 2026
Sometimes, I manage to get it right—recognizing trends, catching the right wave. I've been emphasizing TOAD attacks (Telephone Oriented Attack Delivery), also known as Call Back Fraud, for over two years. I've written about this attack multiple times in the newsletter and included it professionally in my security awareness trainings.
This new report from StrongestLayer confirms that my prediction about the attack's prevalence was accurate.
TOAD is no longer an emerging tactic; it’s become one of the dominant ways attackers bypass enterprise email security.
StrongestLayer shows that more than one in four successful phishing emails now use a phone number as the payload. That means no malicious link. No malware attachment. No exploit kit. Just a callback number.
And that’s precisely why it works.
Traditional Secure Email Gateways (SEGs) are designed to scan URLs, detonate attachments, and score message content for known malicious indicators. TOAD attacks contain none of those. The “weapon” is a string of digits, indistinguishable from a legitimate business contact number. Blocking financial language plus a phone number would cripple normal accounts payable traffic. From an architectural standpoint, these attacks operate in a structural blind spot.
Understanding TOAD requires understanding its layered evasion model.
Layer One: Trusted Delivery. Messages are often sent through legitimate infrastructure such as SendGrid or other reputable platforms. Reputation filtering sees clean domains and allows delivery.
Layer Two: Anti-Scanner. Some campaigns add QR codes inside PDFs or use CAPTCHA gates. Automated sandboxes follow the link, hit a challenge page, and mark the message safe because they never reach the malicious content.
Layer Three: Channel Shift. This is the core of TOAD. The victim calls the number. The social engineering happens over the voice. Credential harvesting, remote access installation, or gift card fraud can unfold during a 20–30-minute conversation. By design, this occurs outside the email system and outside our endpoint detection tools.
For investigators, this means the crime scene is not the inbox. It is the phone call and the subsequent cloud authentication logs. As attackers deliberately move away from malware and toward human exploitation, investigators must adapt accordingly.
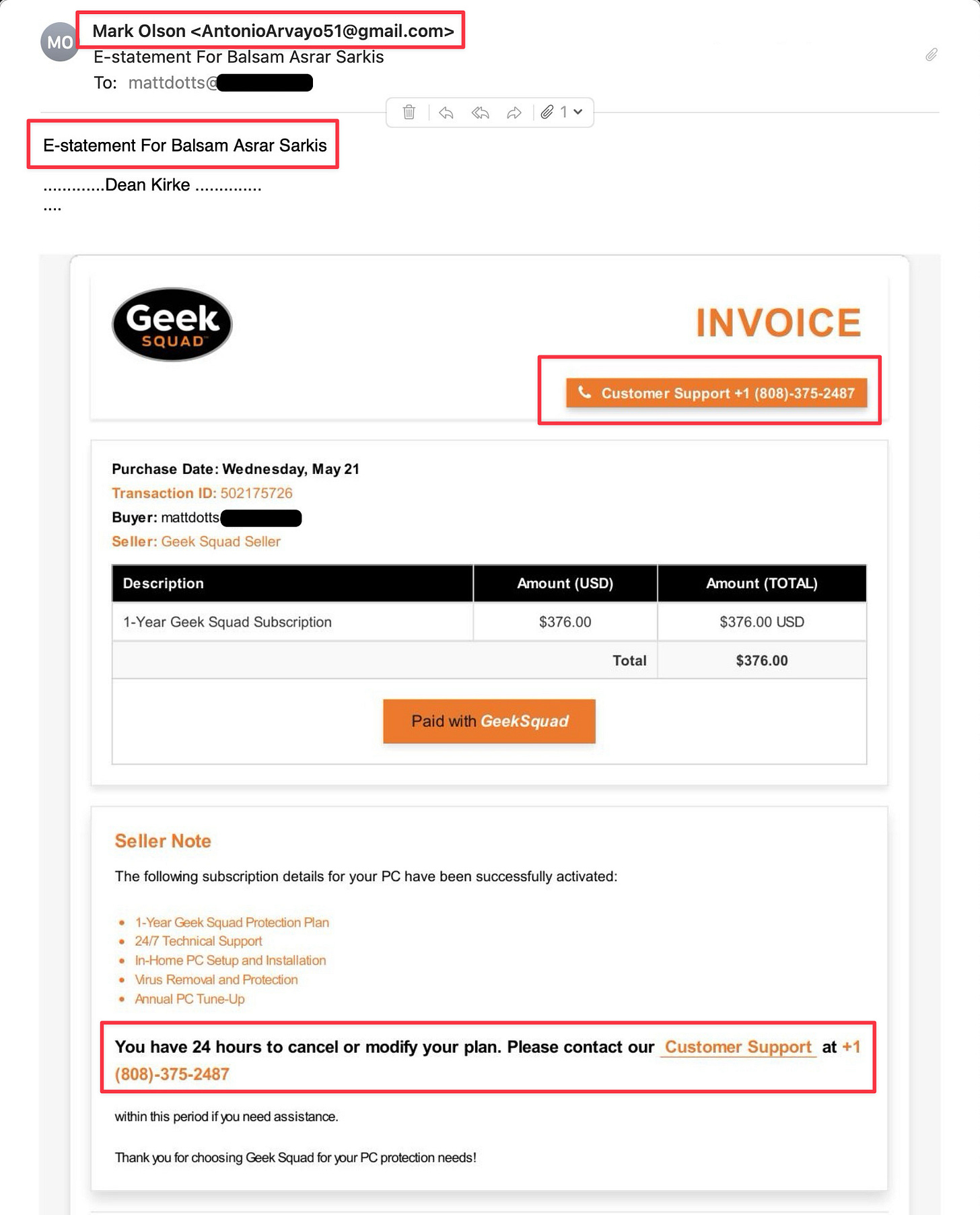
This TOAD attack is designed to make me believe I was wrongly charged for a Geek Squad Protection plan for someone else. But if I act quickly enough, I can cancel the transaction. No links, no email addresses, just a phone number. I just need to call them!
Read the StrongestLayer report: https://cdn.prod.website-files.com/692908f21a0929f1fb06bc04/699df5313a4d214a1d53bd72_2026_Evasion_Technique_Combinations_Research_final.pdf
Unlinking from LinkedIn
I received several comments concerning my take on LinkedIn, included in last week’s issue (275).
Sometimes I think LinkedIn has quietly evolved into professional performance art. It’s just a theater.
People spend enormous amounts of time crafting long-form posts explaining concepts to… other professionals in the exact same field. If most of your network consists of peers who do what you do, who exactly is the audience?
It can feel a bit like delivering a keynote at a firefighter convention about the dangers of smoke inhalation. Important? Absolutely. Groundbreaking? Not so much.
That doesn’t make the content wrong. But it does raise an interesting question: are we sharing insight, or signaling expertise? Are we advancing the conversation, or just making sure everyone sees us advancing it?
There’s nothing inherently wrong with visibility. Thought leadership has its place. But when all of the applause comes from people who already know the script, it’s worth asking whether we’re educating… or performing.
And there’s nothing wrong with performing—obviously, it's something I do every week, but only in the appropriate place.
The News…
Oklahoma man will serve 46 months in federal prison for bank fraud and money laundering. He exploited insider access at multiple financial services companies and a banking software company to steal over $588,000 from accounts at three of the financial institutions. https://www.cutimes.com/2026/02/09/former-credit-union-employee-sentenced-in-588000-insider-fraud-case/
An unknown attacker exploited Anthropic’s Claude AI chatbot to breach multiple Mexican government agencies between December and January, stealing 150 gigabytes of sensitive data, including 195 million taxpayer records, voter information, and government employee credentials. The attacker used Spanish-language prompts to instruct Claude to act as an elite hacker, finding vulnerabilities and automating data theft. Although Claude initially refused some requests, the hacker eventually “jailbroken” it by framing the attacks as legitimate penetration testing and providing a detailed playbook. https://www.siliconvalley.com/2026/02/25/hacker-used-anthropics-claude-to-steal-sensitive-mexican-data/
The AirSnitch attack is a newly discovered Wi-Fi vulnerability that bypasses client isolation, a security feature meant to prevent direct communication between connected devices, by exploiting weaknesses at the lowest network layers. Rather than breaking encryption itself, the attack allows an attacker with access to the Wi-Fi network (or even connected infrastructure) to perform man-in-the-middle attacks, intercept unencrypted traffic, steal credentials, and manipulate data across home, office, and enterprise networks. While the vulnerability affects routers from major manufacturers like Netgear, Cisco, and D-Link, it requires more technical skill than some previous Wi-Fi attacks and can be partially mitigated through VPNs, zero-trust security models, or avoiding untrusted networks, though no complete immediate fix is currently available. https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/
A new federal anti-money laundering rule, effective March 1, 2026, requires reporting of beneficial ownership details (names, addresses, SSNs) for all-cash or non-financed residential real estate purchases made by entities or trusts. The report must be filed with FinCEN within 30–60 days of closing, typically by the closing agent, and title companies may refuse to close without this info. While real estate agents aren’t directly responsible, they should inform clients. FinCEN estimates 800,000–850,000 annual transactions will be affected. https://www.nar.realtor/magazine/real-estate-news/anti-money-laundering-rule-aimed-at-all-cash-buyers-goes-into-effect-march-1
Not victim-blaming here, but how did this situation escalate to the point where you’re paying over 4 million dollars to help your daughter become a model? A photographer was charged with wire fraud and money laundering after allegedly swindling a family out of $4.6 million. Prosecutors say Coyne falsely claimed she was securing modeling gigs for the family’s daughter, but instead used the money for personal expenses such as gambling. https://petapixel.com/2026/03/02/fbi-charge-photographer-with-4-6-million-child-modeling-fraud/
DFIR
The forensic value of Apple Maps. https://forensafe.com/blogs/apple-maps.html
Cool Job
Director of Security Services - Ford Motor Company. https://efds.fa.em5.oraclecloud.com/hcmUI/CandidateExperience/en/sites/CX_1/job/59407
Cool Tool
De-Google yourself - a complete Android-based mobile device operating system that removes all things Google. https://e.foundation/e-os/
Irrelevant
Sign Off
Thanks for coming back after last week’s trash heap of a newsletter. So many typos, including the misspelling of my own domain. Well, I guess it shows that I’m actually writing the newsletter and not AI.
So let’s try this again. You can email me at [matt (at) threatswithoutborders.com]
Matt
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.