Threats Without Borders - Issue 277
Cybercrime Investigation Newsletter, week ending March 8, 2028
How to find a company’s email provider based on the domain.
It’s a 50/50 task. If you solve it correctly on the first try, it’s straightforward. Otherwise, it can become endlessly complex, and you might never find the answer. As I began preparing this piece and designing a workflow to help with your investigations, I realized this isn’t just a simple few-paragraph reply suitable for a newsletter.
So, I’ll give you the easy option first.
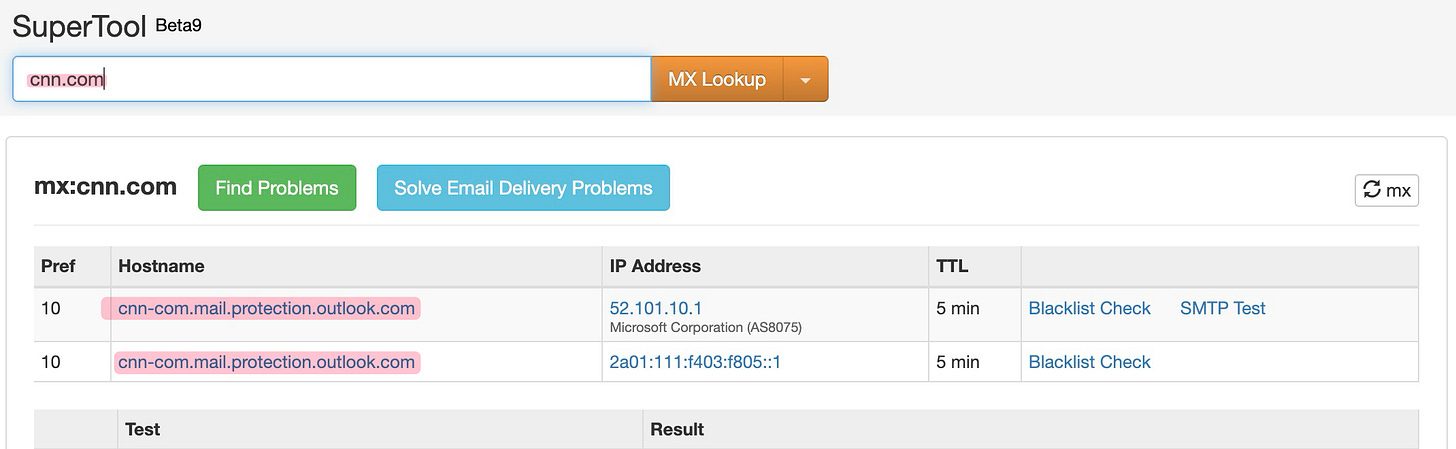
The first step in identifying an organization’s email provider is to check the MX record for the domain, which stands for Mail Exchanger. This record is publicly published in the Internet’s Domain Name System for every organization that receives email, indicating the mail server responsible for accepting their incoming messages. Since it’s publicly accessible, you can look it up without contacting the organization or leaving traces of your search.
To examine it, visit MXToolbox at mxtoolbox.com, enter the organization’s domain name and perform an MX Lookup. The large majority of all business organizations use either Microsoft or Google for email. If the record includes mail.protection.outlook.com, the organization uses Microsoft 365. If it points to google.com or contains aspmx.l.google.com, they use Google Workspace. That’s your answer, and you’re done.
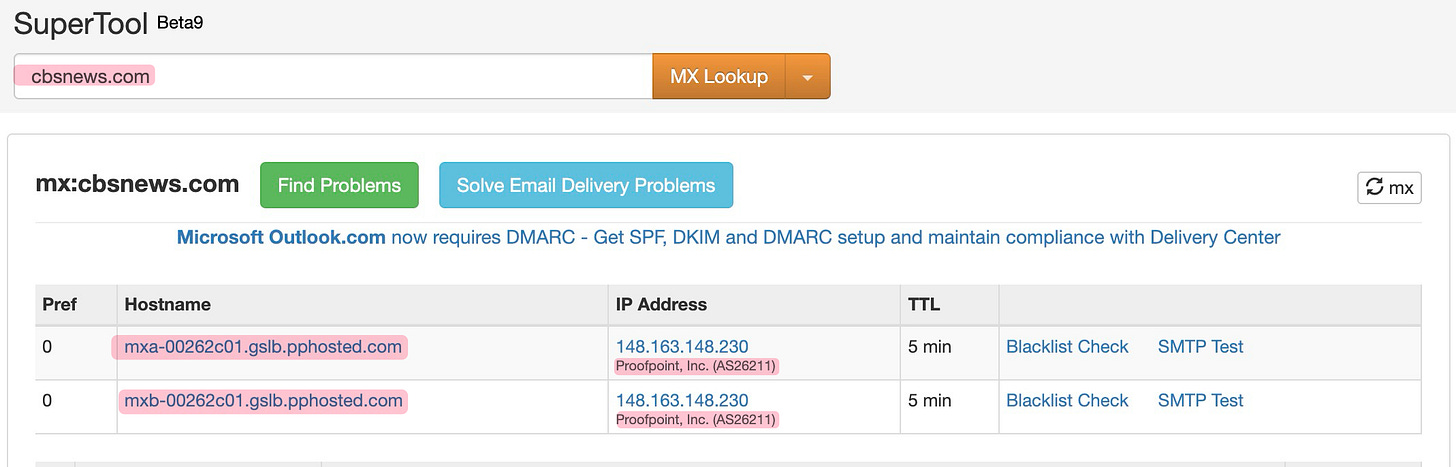
Problems arise if the MX record points to a third-party security gateway instead of Microsoft or Google. Services like Mimecast, Proofpoint, and Barracuda act as intermediaries, filtering spam and malware before forwarding messages. In those cases, the MX record only reveals the gateway used, not the actual mail hosting provider. If your lookup shows hostnames like mimecast.com, pphosted.com, or barracudanetworks.com, you’ll need to investigate further.
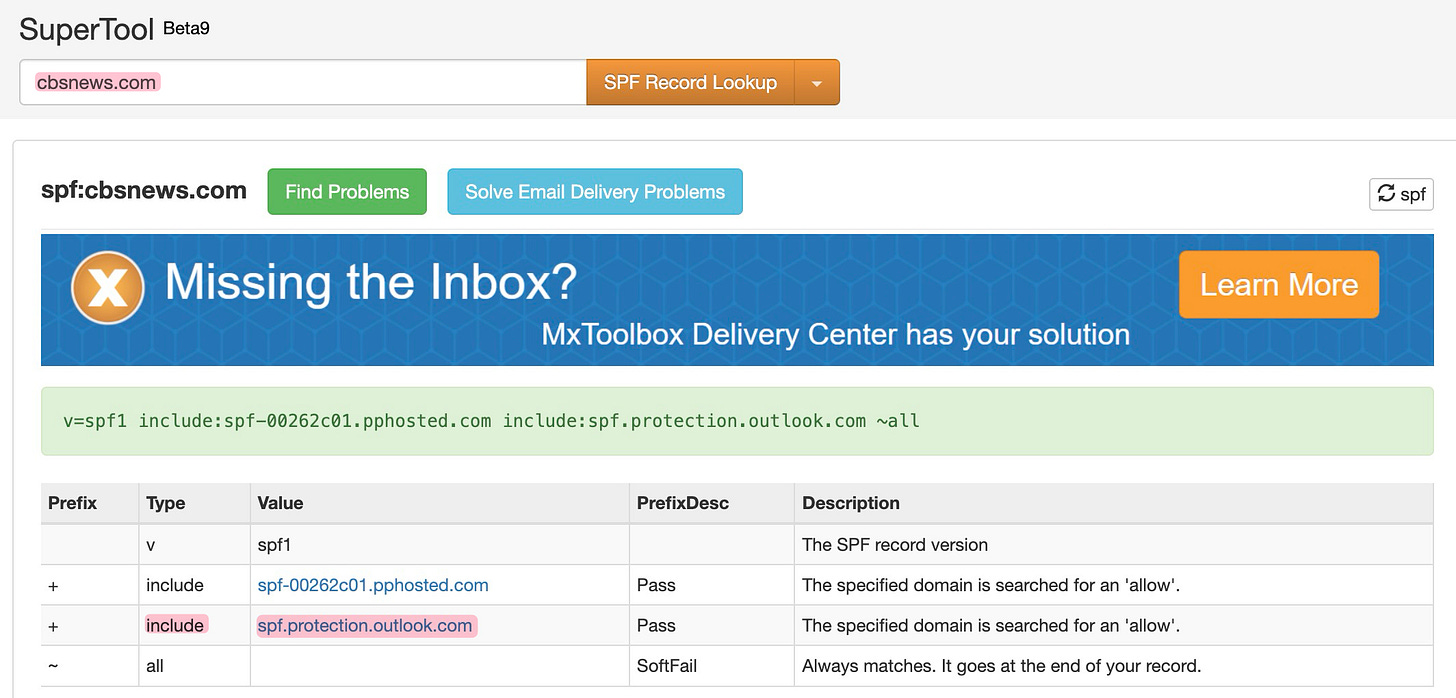
When a security gateway obscures the MX record, we often turn to the SPF record. SPF, or Sender Policy Framework, lists all authorized email sending services for a domain. It aims to prevent email fraud by confirming which servers are legitimate senders, helping mail systems verify message authenticity. Importantly, the list must include the actual mailbox provider; otherwise, legitimate emails could be marked as spam or blocked. This makes the SPF record especially useful during investigations.
To check it, go back to MXToolbox, click the dropdown next to the search button, and select SPF Record Lookup. Enter the same domain and run the search. Although the results may look like a string of technical text, focus on entries starting with “include:”. These indicate external services trusted to send mail for the domain. For example, include:spf.protection.outlook.com suggests Microsoft 365, while include:_spf.google.com indicates Google Workspace — regardless of the MX record.
A security gateway can block incoming mail and hide its destination, but it cannot hide the outbound authorization record. The SPF record must list the real provider, and since it’s public, we can access and read it. Usually, if Phase 1 yields no results, Phase 2 might provide the answer.
The problem is when organizations obscure third-party hosting services or run their own email server. We’ll look at some of those next week.
The News…
The FBI warns of a phishing scam in which criminals impersonate city and county officials to solicit fraudulent permit payments. Victims receive emails containing accurate permit information that request payment via wire transfer, peer-to-peer payment, or cryptocurrency. https://www.ic3.gov/PSA/2026/PSA260309
The White House released its cybersecurity policy in the new document “President Trump’s Cyber Strategy for America." Normally, I’d respond with "Meh," since government policies, papers, and promises are pretty worthless. However, President Trump has established a pretty good track record of following through on his commitments, for better or worse. We should digest this document and prepare to work within its guidelines because it’s likely to be carried out. https://www.whitehouse.gov/wp-content/uploads/2026/03/President-Trumps-Cyber-Strategy-for-America.pdf
Tycoon 2FA was a major “Phishing-as-a-Service (PhaaS)” platform that appeared in 2023 and was developed in 2024 to evade multi-factor authentication using adversary-in-the-middle attacks, capturing live session cookies to access accounts illegally. It was associated with more than 64,000 phishing incidents, affecting nearly 100,000 organizations worldwide. At its height, it accounted for approximately 62% of all phishing attempts blocked by Microsoft. In early 2026, a coordinated operation led by Europol, involving Microsoft, Intel 471, Cloudflare, Coinbase, and others, dismantled the platform’s infrastructure, seizing 330 domains and arresting the alleged ringleader. https://www.intel471.com/blog/born-to-bypass-mfa-taking-down-tycoon-2fa
BLUF: Keep your device updated to the most recent version of iOS. Security researchers at Google discovered an iPhone hacking toolkit called Coruna, originally used by a government customer, that has since leaked and spread to cybercriminals. The kit can compromise iPhones running iOS 13 through 17.2.1 by chaining together 23 vulnerabilities, requiring only that a target visit a malicious website. After its initial discovery in February 2025, the same toolkit was found being used by a Russian espionage group targeting Ukrainians and later by a financially motivated hacker in China. Mobile security firm iVerify linked the tools to the U.S. government, drawing parallels to previously attributed American hacking frameworks. https://cloud.google.com/blog/topics/threat-intelligence/coruna-powerful-ios-exploit-kit
The FBI has extradited a 28-year-old Bangladeshi from Malaysia to Alaska to face charges related to an international child sexual exploitation ring. Indicted in 2022 by an Alaska federal grand jury, the man is accused of using Instagram and Snapchat to coercively obtain sexually explicit material from hundreds of minors across the U.S. and internationally. He faces multiple charges, including conspiracy to produce child pornography, child exploitation enterprise, cyberstalking, and wire fraud. If convicted, he could face 20 years to life imprisonment. Kudos to the BU, Alaska State Police, and Anchorage PD for wrapping this guy up. https://www.justice.gov/usao-ak/pr/bangladeshi-national-make-initial-appearance-following-arrest-fbi-international
Who says crime doesn’t pay? Retail crime certainly seems to pay. This Ohio woman defrauded Home Depot of $266,699 through 1700 fraudulent returns. She was sentenced to 180 days in jail and five years of community supervision. Oh, and restitution, but we all know that will likely never happen. So, a quarter of a million dollars to sit in jail for 180 days? Some might say that’s a steal. https://www.cleveland19.com/2026/03/05/ohio-womans-multi-state-retail-fraud-scheme-created-266699-fake-store-credit-police/
DFIR
I once testified as an expert witness in a trial concerning the recovery of dashcam video evidence. I removed the microSD card from the device, cloned it, and then played the mp4 file to isolate the time period of the vehicle crash. It takes an expert to explain that process, I guess. In this post, SalvationData goes a little deeper into the process. https://www.salvationdata.com/product-tips/dashcam-video-recovery/
Mail Call
“Matt, don’t hate the player, hate the game. Personal branding is now a professional requirement, and LinkedIn is the most efficient place to do it.” - TF
Speaking of LinkedIn
I’ve been notably resistant to freaking out about AI being used to facilitate cybercrime, noting that the old methods still work just fine. But every day I become more bullish.
TrendAI researchers demonstrate how publicly available LinkedIn data can be rapidly weaponized into highly targeted phishing attacks using AI tools. The researchers built a proof-of-concept system that automates the collection of public LinkedIn posts and images, analyzes them for contextual insights, and generates detailed employee profiles. Using AI, the tool identifies key professional interests, creates personalized marketing emails, discovers likely email addresses, and even generates realistic phishing websites tailored to the target’s expertise—all within 30 minutes.
Cool Job
Fraud Investigator, PSECU. https://psecu.wd12.myworkdayjobs.com/PSECU/job/Harrisburg-PA/Fraud-Investigator_JR100773
Security Investigations Manager, Anduril. https://job-boards.greenhouse.io/andurilindustries/jobs/5051653007
Cool Tool
Find Flock cameras. https://deflock.org/
Irrelevant
System76 makes computers that run the Linux operating system and they are the publisher and maintainer of the pop_os! operating system. I’ve used both, hardware and software.
Colorado’s Senate Bill 26-051 and California’s Assembly Bill No. 1043 mandate that operating systems must report age brackets to app stores and websites. When someone creates an account on a computer, they are expected to be 18 or older and confirm their age, whether for themselves or their child. In reality, this regulation implies that individuals under 18 are generally not supposed to set up their own computer accounts.
The law requires technology providers to verify that all users are of legal age. While the Internet has harmful content and children need protection, it is ultimately the parents’ responsibility to provide guardrails. Stop expecting technology and Internet Service Providers to act as parents.
The CEO of Colorado-based System76 offers a clearer, better-argued case for why we should probably oppose these age-verification laws.
https://blog.system76.com/post/system76-on-age-verification
Sign Off
I felt something I haven’t in a long time this week. The warmth of the sun. Yeah, that big yellow orange thing in the sky. It’s still there and doing well. And the microdose of vitamin D has given me some hope we’ll pull out of the long cold winter season.
Thanks for staying with me each week, even when the newsletter is trash.
See you all next week.
Matt
“EVERY DAY YOU WAIT IS ANOTHER DAY YOU WON’T GET BACK.”
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.