Threats Without Borders - Issue 283
Cybercrime Investigation Newsletter, week ending April 19, 2026
I recently had a question about an IP address that resolved back to “iCloud Private Relay,” which is more information than is usually provided, since most of the time addresses just resolve to “Cloudflare” or “Akamai.” Unfortunately, for most investigations, this also resolves to a roadblock.
Apple introduced Private Relay as part of iCloud+, and most people think it’s Apple’s VPN service. It isn’t a VPN. It’s more accurate to call it a dual-hop proxy. The service is designed to make sure no single entity, not even Apple, knows both who you are and what you’re looking at. Apple's inclusion in that “no single entity” part is either admirable or politically convenient, depending on your level of cynicism.
When a user browses in Safari with Private Relay enabled, their traffic takes a two-stop detour before reaching its destination. First, it hits an Apple server. Apple sees the user’s real IP address, but can’t see where they’re going because the DNS request is encrypted. The traffic is then handed off to a second relay server operated by a third-party partner like Cloudflare, Akamai, or Fastly. That server knows the destination but has no idea who the user is. The website at the end of that chain sees a generic, temporary IP address shared by potentially thousands of other users in the same general region.
Nobody has the whole picture. That’s the whole point.
Private Relay protects only Safari browsing and encrypts DNS queries on the device.
It does not protect Third-party browsers like Chrome, Edge, or Firefox. Instagram, Facebook, email, banking apps, and most other apps on the device are also unprotected. In the absence of some additional masking technology, those will still phone home with the user’s real IP address.
So when trying to unmask a web browser user, our standard move -- get the IP, search warrant to the ISP, get the subscriber -- hits a wall. The destination logs a relay egress IP shared by thousands of users. The ISP can see the device was connected to Apple, but has no record of which sites were visited. And the relay partner doesn’t store the incoming Apple IP in a way that ties it to the outgoing destination. Nobody has the full picture. By design.
There are still some investigative avenues.
First, Apple publishes a list of all Private Relay egress IP ranges at https://mask-api.icloud.com/egress-ip-ranges.csv. Run any suspicious source IP against that list before spending resources on an ISP subpoena. Know what you’re dealing with upfront.
Second, Private Relay only masks the IP and DNS. Browser fingerprinting artifacts such as canvas fingerprinting, screen resolution, and installed fonts can still tie a specific Safari instance to activity across multiple sessions.
Third, look for cross-app leakage. If your subject used any other app on that same device, such as a different browser, a social media app, or any other service for communication across the Internet, those connections bypassed the relay entirely and may have logged the real IP with those respective servers.
iCloud Private Relay is a headache, a roadblock for sure, but maybe not a dead end. It breaks the attribution chain rather than eliminating it, but sometimes broken chains can still be put back together.
The News
Microsoft explains how to prevent domain compromises through “predictive shielding”. Predictive shielding in Microsoft Defender’s automatic attack disruption helps prevent the spread of identity-based attacks by acting before stolen credentials are fully exploited. Rather than waiting for malicious activity on an account, it detects early signs of credential exposure, such as high-confidence signals of credential theft, and proactively restricts potentially compromised accounts. https://www.microsoft.com/en-us/security/blog/2026/04/17/domain-compromise-predictive-shielding-shut-down-lateral-movement/
Think you won’t get bitten by a malicious insider? Cryptocurrency exchange, Kraken, is standing up to extortionists and refusing to pay their ransom demands. Kraken experienced two extortion attempts stemming from “inappropriate” access by support team members, not external breaches. Approximately 2,000 accounts were potentially compromised. https://www.blockhead.co/2026/04/14/kraken-refuses-extortion-demands-after-criminal-group-films-internal-systems/
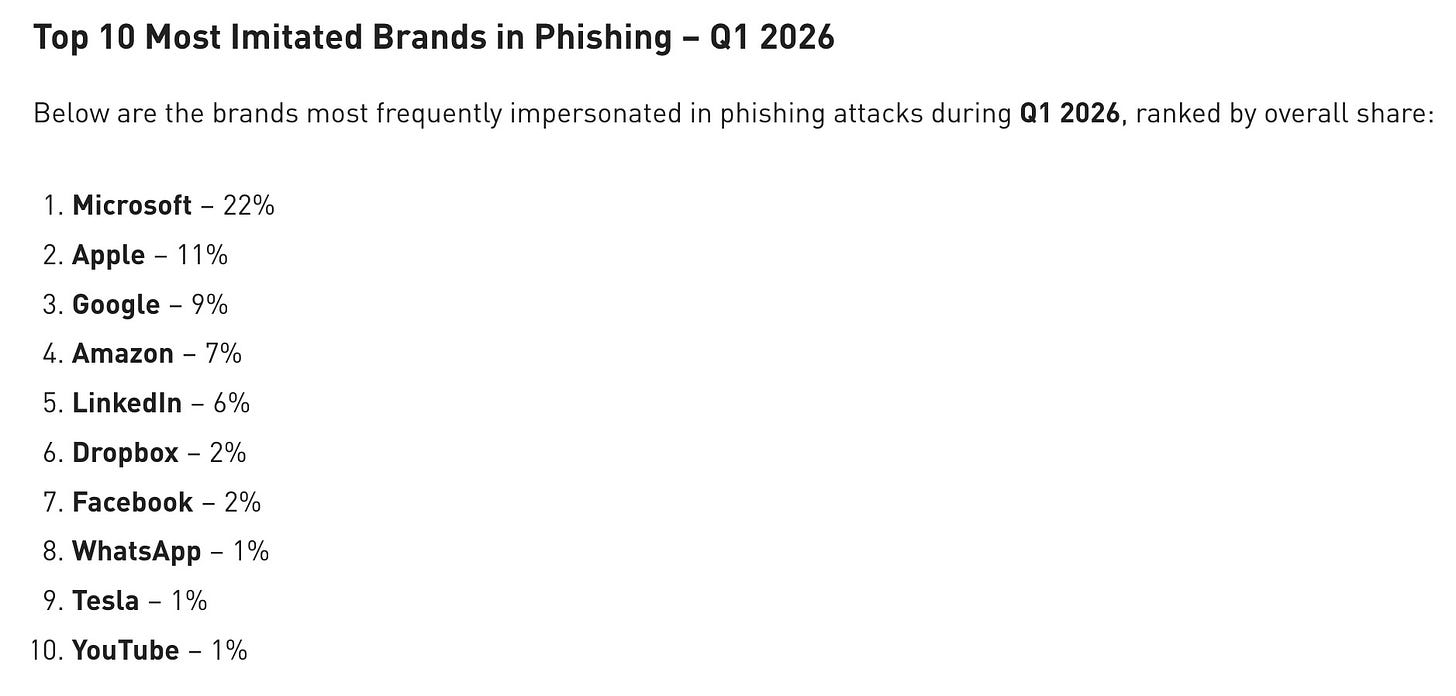
I recently shared a report from another threat intel company that claimed Docusign is now the most imitated brand in phishing attacks. Checkpoint doesn’t even list them in the top ten. Regardless, I’m sure this list is applicable.
So, you want to be a darknet drug lord? https://pastebin.com/raw/GrV3uYh5
The TidBITS public Slack group (SlackBITS) is being closed after a social engineering attack where the attacker impersonated author Glenn Fleishman by duplicating his profile and display name, then sent a direct message to another user to trick him into installing the OSX.Odyssey infostealer malware. https://tidbits.com/2026/04/18/shutting-down-slackbits-after-impersonation-based-malware-attack/
Wine Fraud - Yep. A 59-year-old UK citizen was sentenced to 10 years in federal prison for orchestrating a $97 million wine fraud scheme. Posing as the CFO of a fictitious company, the man and a co-conspirator deceived over 140 investors worldwide by falsely claiming to broker loans secured by high-value wine collections. In reality, the operation was a Ponzi scheme that used new investor funds to pay fake interest to earlier investors. Of the $97 million collected, only ~$14 million was returned, leaving victims with losses exceeding $83 million. https://www.justice.gov/usao-edny/pr/united-kingdom-citizen-sentenced-10-years-prison-97-million-wine-fraud-scheme
Feedback
Send Feedback to matt(at)threatswithoutborders.com
Losing Argument
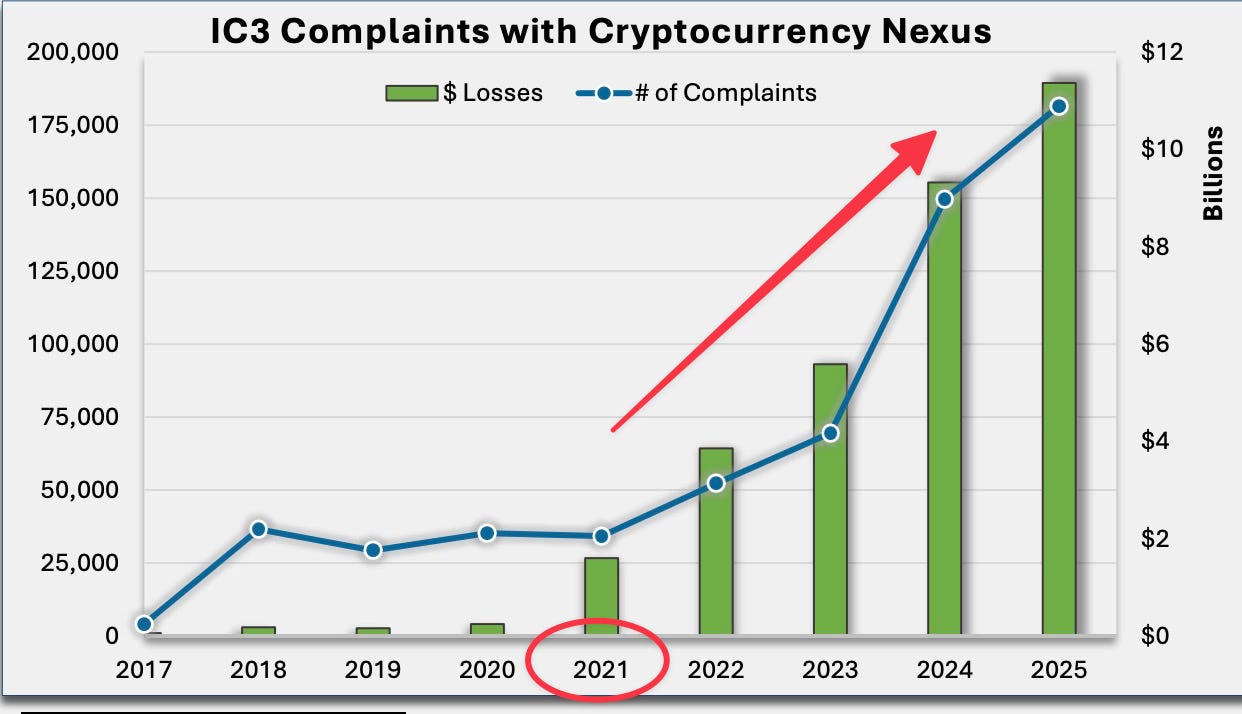
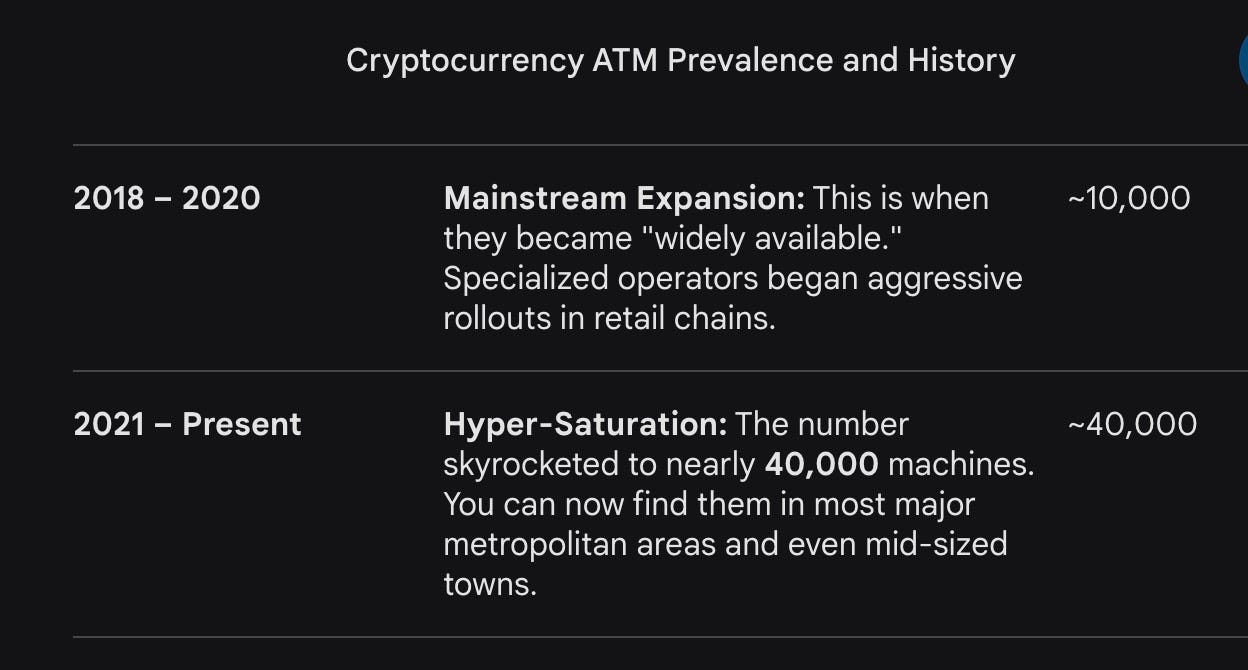
This is for anyone who denies a connection between the rise in cryptocurrency use for fraud and the proliferation of cryptocurrency ATMs.
Cryptocurrency complaints were relatively flat until the first jump in 2021. And then it skyrockets over the next four years.
And sure enough, the Gemini tells us there was a huge influx, or “Hyper Saturation,” of machines beginning in 2021.
Cool Jobs
Director of IT Security - Denver Broncos Football Team. https://job-boards.greenhouse.io/denverbroncosteamllc/jobs/5191274008
Cool Tools
Those who attended my recent talk on quickly triaging websites to determine legitimacy or attribution know that Whois has been replaced by RDAP. The name changed, but the data remains the same. And you might need to go back in history to find out not Who Is, but Who Was! ARIN’s WhoWas service provides historical registration information for IP addresses and ASNs. (Registration required) https://www.arin.net/reference/research/whowas/
Irrelevant
Claude can’t use a typewriter. College instructor turns to old school typewriters to curb the use of AI for assignments.
“What’s the point of me reading it if it’s already correct anyway, and you didn’t write it yourself? Could you produce it without your computer?” said Phelps.
Sign Off
I’ve come to the realization that I’m a domain hoarder. Domain-rich but cash-poor, I guess. Every time I think of an awesome web domain name, I purchase it, usually with the idea of starting a business someday. But that never happens, and I just keep paying the yearly domain registration fees. It’s become expensive enough that I’ve come to a reckoning. I need to give up some, but it feels like giving up on ideas.
Oh, that’s a great name…domainhoarder.com!
Have a great week. See you all next Tuesday.
Matt
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.
cybercrime cybersecurity cyficime cyber fraud investigations aml osint