Threats Without Borders - Issue 284
Cyber-Financial Crime Investigation Newsletter, week ending April 26, 2026
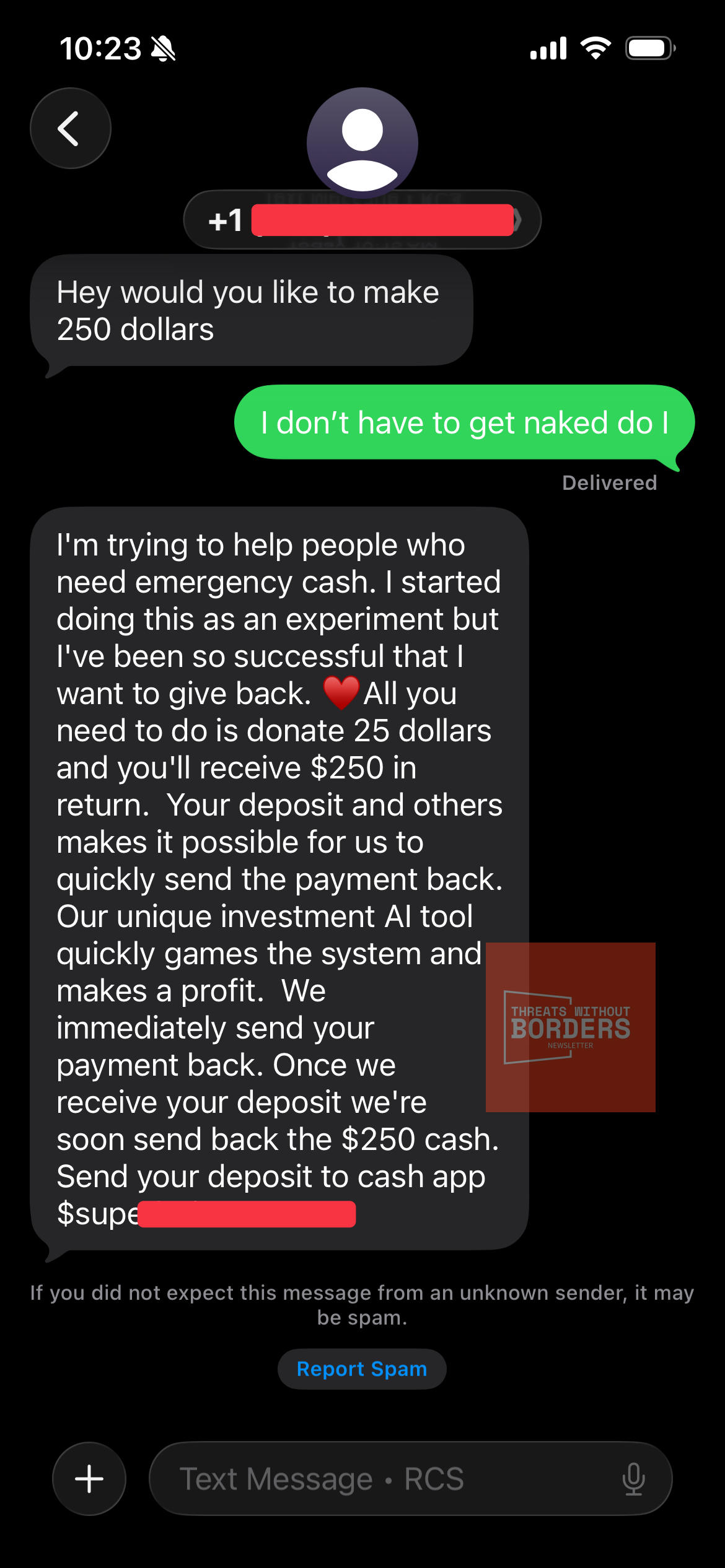
I had a fun conversation this week.
It’s called a cash-flipping scam, and this version has been dressed up with an artificial-intelligence angle to make it sound sophisticated. It isn’t. But the people running it are smarter than you might think, and the way they’ve structured it creates some real challenges for victims and investigators.
The target gets an unsolicited text from a stranger promising easy money. The script goes something like this: send me $25, I’ll use my AI tool to flip it, and I’ll send you back $250. Simple, fast, and painless. Of course, the moment the money moves, the scammer either disappears or comes back asking for a little more before the payout arrives. There is no AI. There is no payout. Only fraud.
The $25 is important because the low dollar amount is not random. It’s a calculated decision. The people running these scams have figured out something that works in their favor at almost every level of the criminal justice system.
At $25, most victims are embarrassed, frustrated, and ultimately unwilling to take time out of their day to file a police report over a loss that won’t even cover their gas to get to the station. And honestly, can you blame them?
So the first filter is self-reporting; most of these never get reported at all.
The second filter is law enforcement. Even when a report is filed, no investigator opens an active investigation into a $25 fraud. The caseload doesn’t allow for it.
The third filter is the prosecutors. Even if someone handed a DA a complete, airtight case involving a $25 theft by a non-local suspect, no prosecutor would entertain charging, let alone extraditing, a defendant over such a de minimis loss. The scammers know this. They have built their entire business model around staying below the threshold that triggers a system response.
Live on the West coast of the country and scam people on the East coast for low dollar amounts... bulletproof.
What they’re actually doing is running this scheme at volume. A hundred victims at $25 each is $2,500. A thousand victims is $25,000. The individual loss is invisible to the system, but the aggregate is very real money.
These scams almost always use peer-to-peer payment apps like Cash App, Venmo, or Zelle, and that choice is deliberate too. P2P transfers are fast, feel casual, and are extremely difficult to reverse once completed. There’s no effective dispute process, unlike with a credit card. When the money moves, it’s gone.
But these accounts don’t exist in isolation. Cash App accounts must be verified with real identity details, including name, date of birth, and Social Security number. Additionally, they are connected to a real bank account. Somewhere within this chain, there’s a real person involved. It could be the scammer themselves or a money mule, but in either case, a person is associated with a financial institution that keeps records. Law enforcement with proper legal authority can serve a search warrant on Cash App and the linked bank to access this information (Yeah, I know, don’t hold your breath). The data is available; the key question is whether pursuing it is worth the effort, and that leads me to the most crucial point.
A single $25 case will go nowhere. But if you bring a prosecutor a case showing that the same Cash App tag, the same phone number, or the same script was used against 200 victims across multiple jurisdictions, resulting in $5,000 or $50,000 in total losses, that is a different conversation entirely.
Investigators need to connect with each other early and often. When you see one of these cases, get it into IC3 at ic3.gov and the FTC at reportfraud.ftc.gov immediately and make sure your victims do too. Include the Cash App tag, the phone number, the exact wording of the message, and any transaction IDs. Then reach out laterally—to investigators in neighboring jurisdictions, to fraud units in other agencies, and to your financial crime information networks. Ask whether anyone else is seeing the same tag or the same number.
The scammer is betting that each of us will look at $25 and walk away. The way we beat that bet is by refusing to work in silos. The case that can’t be built by one investigator on one complaint can absolutely be built when ten investigators across five states are looking at the same actor. Aggregate the losses, aggregate the evidence, and suddenly the math changes for everyone.
The News
Tennessee joins Indiana in banning cryptocurrency ATMs. https://www.yahoo.com/news/articles/tennessee-becomes-second-state-outlaw-204113466.html
Toronto Police have arrested and charged three men with 44 offenses following an investigation into the first known use of a mobile SMS blaster device in Canada. This technology mimics cellular towers to intercept phone calls and send fraudulent text messages that appear to come from trusted organizations such as banks, often directing victims to fake websites to steal personal and financial information. The investigation, called Project Lighthouse, began last November and detected thousands of device connections and over 13 million network disruptions across the Greater Toronto Area.
https://torontosun.com/news/local-news/toronto-cops-cybercrime-tool-sms-blaster-spam-phones
A man from Baltimore faces charges including wire fraud, mail fraud, aggravated identity theft, theft of government property, and making false statements. As a former Social Security Administration (SSA) customer service representative, he had access to sensitive SSA databases with personally identifiable information of benefit claimants. The indictment reveals that between February and April 2023, he planned and carried out a scheme to defraud the SSA. He fraudulently obtained Supplemental Security Income (SSI) benefits intended for others, using them for himself and his associates. He targeted claimants with mental health diagnoses, modifying their records to include bank accounts he controlled and his residential address, enabling him to divert their SSI payments. Additionally, he altered the benefit payment dates in SSA’s system, creating back payments in the claimants’ names, and redirected these payments to his accounts. https://www.justice.gov/usao-md/pr/former-social-security-administration-worker-charged-disability-funds-theft-scheme
Holy insider threat! A US special forces soldier was arrested for allegedly betting on the capture of Venezuelan President Nicolás Maduro, earning $400,000. Prosecutors claim he was involved in planning the mission and used insider information to place the bet. https://www.cnn.com/2026/04/23/politics/us-special-forces-soldier-arrested-maduro-raid-trade
It’s Spy vs. Spy. Apple has introduced a software update for iPhones and iPads to fix a serious bug that let law enforcement recover deleted or expiring messages by accessing cached notification content stored on the device for up to a month. The flaw, revealed when the FBI used forensic tools to retrieve deleted Signal messages, was caused by notifications that kept message content in the OS database even after the messages were deleted. Apple fixed this by making sure notifications marked for deletion are no longer stored unexpectedly. The update has also been applied to older iOS 18 versions to enhance user privacy. https://techcrunch.com/2026/04/22/apple-fixes-bug-that-cops-used-to-extract-deleted-chat-messages-from-iphones/
Kudos to law enforcement in Pittsburgh, PA, for their successful effort. Over two days, federal, state, and local authorities collaborated in the Pittsburgh area, resulting in the seizure of nine illegal card-skimming devices. This operation potentially prevented over $9 million in fraud losses for the public. The U.S. Secret Service, in coordination with Allegheny County Police, Pittsburgh police, the state attorney general, the U.S. Postal Inspection Service, and the state inspector general, visited 272 locations on Monday and Tuesday. During these visits, they examined 883 point-of-sale terminals, 775 gas pumps, and 170 ATM terminals. https://triblive.com/local/secret-service-led-operation-nets-9-credit-card-skimming-devices-in-pittsburgh-area/
The Talos group reports that phishing has reemerged as the most commonly observed means of gaining initial access, accounting for over a third of their engagements in which initial access could be determined. Phishing has not been the top vector for initial access since Q2 2025. https://blog.talosintelligence.com/ir-trends-q1-2026/
ADT confirmed a data breach that resulted on the loss of customer data, including names, contact details, dates of birth, and the last four digits of Social Security numbers. ShinyHunters has claimed to possess 10 million records and threatened to leak them unless a ransom is paid. https://therecord.media/ADT-data-breach-cyberattack
Feedback
Send Feedback to matt(at)threatswithoutborders.com
Investigations
The Supreme Court will hear oral arguments in Chatrie v. United States, a case examining the use of “geofence warrants” by law enforcement to obtain location data from tech companies like Google. The case centers on Okello Chatrie, who was convicted of bank robbery after authorities used a geofence warrant to identify his cellphone location near the crime scene. Chatrie argues that the warrant violated the Fourth Amendment by conducting a search without sufficient probable cause and that he had a reasonable expectation of privacy in his location data, which the government should not be able to access without a warrant. The government contends that Chatrie had no such privacy expectation because he voluntarily shared his location data with Google, and that the warrant was not a general search but a targeted request.
https://www.scotusblog.com/2026/04/court-to-hear-argument-on-law-enforcements-use-of-geofence-warrants/
I absolutely endorse this message:
Cool Jobs
Manager of Security Awareness and Learning, Vanguard. https://vanguard.wd5.myworkdayjobs.com/en-US/vanguard_external/job/Malvern-PA/Manager--Security-Awareness-and-Learning_177094
Lead Investigator, National Basketball League. https://careers.nba.com/job/NBANBAUSJR000581EXTERNALENUS/Lead-Investigator
Cool Tools
“Upload a screenshot or photo and get clue-based location reasoning in seconds”. Probably not. But it’s currently free, so give it a try. https://reverseimagelocation.com/
DorkEye is an advanced automated dorking and OSINT recon tool that leverages DuckDuckGo. (Fantastic documentation!) https://github.com/xPloits3c/DorkEye
Irrelevant
Are you an Advil person or a Tylenol person? Acetaminophen, ibuprofen, and what doctors probably want you to know. https://asteriskmag.com/issues/14/the-mystery-in-the-medicine-cabinet
Sign Off
Thanks for reading this far. Recently, Google started blocking email tracking pixels, which Substack relies on to track open rates. Many other email services have also blocked these trackers, and now Google Gmail has joined them. My open rate was already inconsistent due to these controls, and now it’s completely useless metric. I really don't know how many subscribers read the newsletter each week. So, I’ll just keep throwing it at the wall and hoping for the best.
Matt
“THAT SHIT THAT HAPPENED YESTERDAY, HAPPENED YESTERDAY. MOVE ON.”
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.
cybercrime cyficrime financial fraud investigations osint aml cybersecurity