Threats Without Borders - Issue 285
Cybersecurity Investigations Newsletter - Week ending May 3, 2026
I’m frequently asked in my community presentations if PDFs are “safe” to open. As usual, my answer is something to the effect of “maybe”.
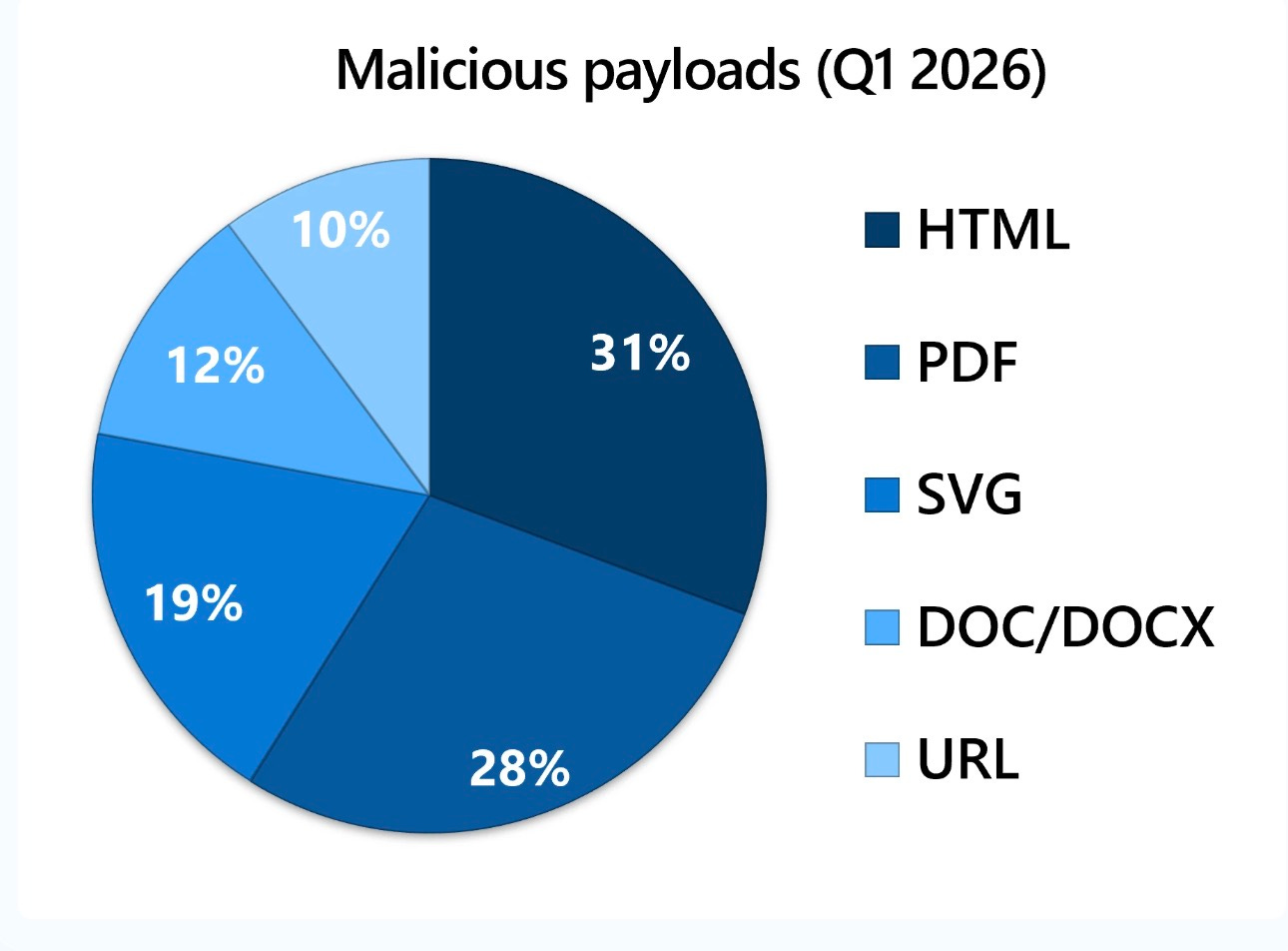
As the Q1 2026 Email Threats Landscapes Report from Microsoft details, PDFs are becoming one of the main malicious payloads for attackers, second only to HTML files
PDFs have become one of the most effective tools for the cybercriminal, not because they look dangerous, but because they look normal. We all use them every day! In most workplaces, PDFs are the default format for invoices, resumes, reports, and contracts. That familiarity creates trust, and attackers take full advantage of it.
But a PDF isn’t just a simple document. It’s a “rich” file format capable of running code, embedding other files, and interacting with users. That means a PDF can behave more like a small program than a static page.
Attackers exploit this in several ways, including embedded JavaScript that runs automatically when the file is opened. If the user’s PDF reader has a vulnerability, that script can attempt to exploit it and gain control of the system. In other situations, the PDF acts as a delivery mechanism, sometimes called a “dropper.” The file itself may appear harmless, but it triggers a download of malware from an external server once opened.
The most common method, however, isn’t a technical exploit; it’s simple visual deception. Examples include fake buttons, where a PDF displays a message like “This content is encrypted. Click here to decrypt.” Clicking the button redirects the user to a counterfeit login page (such as a spoofed Microsoft 365 portal) to steal credentials. Another method is the favorite tool of every marketer, URL shorteners. Malicious links are often concealed behind shortened URLs or legitimate-looking text to avoid detection by email security systems.
From a security standpoint, PDFs are difficult to detect and block for a few key reasons. First, attackers can hide or encrypt parts of the file, making it hard for email security tools to inspect the contents. Second, PDFs can be large and complex, and some systems limit how deeply they scan files to avoid slowing down email delivery.
The result is a perfect storm: a trusted file type, powerful built-in features, and technical complexity that challenges traditional defenses.
So, back to the question, is that PDF safe to open?
The default test for the everyday email users is, do you know the sender? But you need to consider that even a known sender might have a compromised account. The better test is, were you expecting the document? If not, use the phone and call the sender. Oh, and don’t call the contact number included in the email. You might be calling the bad guys!
Read the full Microsoft Report: https://www.microsoft.com/en-us/security/blog/2026/04/30/email-threat-landscape-q1-2026-trends-and-insights/
The News
Varonis Threat Labs discovered Bluekit, a phishing kit offering 40+ website templates, automated domain services, and add-ons, including AI assistants and voice cloning. While the platform is good, it’s not as good as promised. https://www.varonis.com/blog/bluekit
Scott Lang from Spur contends that relying solely on a single off-the-shelf fraud score to assess IP risk is restrictive. This approach tends to condense complex, multidimensional data into a static “black box” number that lacks necessary context and adaptability. He argues that security teams should focus on detailed IP intelligence features, such as data center locations, VPN links, and geographic discrepancies, to develop transparent and customizable risk models aligned with their specific organizational needs and risk tolerance. By moving away from a universal score towards a “glass box” methodology, organizations can make finer decisions, like initiating additional authentication steps or blocking traffic, based on genuine underlying signals rather than an opaque overall score. https://spur.us/blog/ip-risk-scoring-vs-ip-context
The FBI issued a PSA warning that cyber threat actors are impersonating legitimate businesses to hijack freight and steal high-value shipments. Since 2024, these actors have gained unauthorized access to computer systems, posing as victim companies and redirecting goods for resale. In 2025, estimated cargo theft losses in the United States and Canada surged to nearly $725 million. https://www.ic3.gov/PSA/2026/PSA260430
I’m more concerned about having my voice recorded in a permanent file, but these authors argue that patients should refuse consent for “AI” scribing tools in healthcare settings due to significant privacy risks, the potential for reduced openness during consultations, and the likelihood of automation bias leading to inaccurate medical records. They contend that charting is an essential part of the care process itself, and that replacing it with automated drafts degrades both immediate and long-term patient outcomes. https://buttondown.com/maiht3k/archive/why-you-should-refuse-to-let-your-doctor-record/
It’s Conference Season
I originally published this back in 2024, but since it’s conference season, let me remind you of the most terrible conference attendee – Conference Question Guy. And it’s always a guy.
Gotcha Guy attempts to put the speaker in a bad spot by asking a question about some obscure or little-known technical aspect of the speaker’s topic. The question’s intent isn’t to elicit more knowledge or spur conversation but to trick the speaker and make them look poor in front of the audience.
Test the Speaker’s Knowledge Guy, much like Gotcha Guy, this question asker is already knowledgeable about the topic and asks a question that he already knows the answer to. He’s a more benign version of Gotcha guy.
You can immediately spot Look How Smart I Am Guy as he’s on the edge of his seat the whole talk, and only an ounce of self-restraint is keeping him from stepping up on stage. His head is nodding or shaking throughout the entire talk, and he usually makes statements to those around him. His hand will be the first one up after the talk. His proposed question is usually a softball, but will be constructed to allow him to follow up with a more detailed and technical retort to demonstrate his mastery of the speaker’s topic.
While Mask Guy’s commitment to public health is admirable, no one can hear the question, including the speaker. The easy solution is just slightly to pull the mask down when asking the question, but since they don’t, they just come across as a virtue-signaling asshole.
Mansplaining Guy is a particularly dreadful species; the Mansplaining Guy targets female speakers and uses their questions as a way to lecture about a particular topic point he feels the speaker didn’t thoroughly explain or doesn’t completely understand.
Political Statement Guy usually wears the requisite noble cause t-shirt or some slogan buttons on his jacket. “How will this be interpreted by the [insert politician] government, considering their failure to…”, “Don’t you think this is all irrelevant, considering there are children dying on Côte d’Ivoire cocoa farms?“, “Isn’t this an assault on the 1st Amendment?” “Have you seen any evidence that this might lead to the loss of the Arctic ice shelf…”, AHHHHHH – Please just stop.
Complain About My Employer Guy uses their question to passively-aggressively criticize their own employer or supervisor, framing it to get the speaker to agree with their assertion.
To clarify, speakers crave questions. There’s nothing worse than finishing your conference talk with “and now I’ll take any questions!” only to get blank stares and silence. Questions from your audience show they were listening to your words, and your ideas resonated, or at least got them thinking.
Please challenge your conference speakers, but do it for the right reasons.
Don’t be Conference Question Guy. Everyone hates that guy.
Feedback
Send Feedback to matt(at)threatswithoutborders.com
dfir
Steve Whalen from Sumuri digs into Mac metadata. https://sumuri.com/what-your-mac-forensic-tool-isnt-telling-you-about-metadata/
No subscription fees. No ads. No sponsored posts. Even the snark is free.
How about helping us grow?
Cool Jobs
Director of Risk and Payment Options, BetMGM. https://betmgminc.wd5.myworkdayjobs.com/en-US/BetMGM/job/Director--Risk-and-Payments-Ops_JR100645
Cool Tools
Obtain the results from 100 different search engines with a single search: https://www.100searchengines.com/
Irrelevant
The end of an era…Jeve’s retires as Ask shuts down after 25 years. https://www.ask.com/
Sign Off
I've likely been the most persistent squeaky voice regarding the locations of the Keystone Connection conferences over the years—almost as much as my ongoing complaints about the event’s name. This year, however, Steve Lenderman and his team got it right, hosting the event at a fantastic venue in a prime location. And of course, I won't be able to attend due to other commitments.
Anyways…you should attend. And you still have time to register!
https://keystonekonnection.com/
Matt
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.