Threats Without Borders - Issue 286
Cyber-Financial Crime Investigation Newsletter, week ending May 10, 2026
There’s a special kind of confidence that exists on LinkedIn. Someone shares an article with a dramatic headline, adds “Important read!” or “Everyone needs to see this,” and suddenly the post starts bouncing from connection to connection like a digital game of phone-a-friend.
And this week, I almost fell for it myself.
One of my connections shared a post from a well-known anti-fraud organization that is usually pretty solid. Buried inside was a link to an article about how cybercriminals are using AI to craft scams and phishing attacks. On the surface, it sounded reasonable as AI is being used by criminals. So I was about two clicks away from hitting the repost button myself.
But then I did something crazy, I read the article.
Not the headline. Not the summary. Not the one-line hot-take above the share. The actual article.
The piece was written by a company selling an AI detection product for fraud prevention. Their “research” conveniently supported the urgent need for the exact service they happen to sell. The article sprinkled in just enough truth to sound credible, then fired up the hype machine and drifted straight into panic-porn marketing.
It wasn’t education. It was advertising dressed up as analysis.
I’m sure the person who shared it trusted the person they got it from. And that person probably trusted their connection. By the time it reached my feed, it was basically a share of a share of a share of a share, with everyone assuming someone else had done the homework.
Nobody did, and this happens constantly on LinkedIn. Content becomes heavily nested through reposts, and eventually, the original source becomes little more than a decorative attachment. People aren’t evaluating the information anymore. They’re evaluating the social credibility of the person sharing it.
“If Bob gave it a red 100 emoji, it must be good.” Meanwhile, Bob read exactly three sentences and a bullet point.
That’s why I read every article I include in the newsletter. Including an article doesn’t mean I endorse it or the author. I don’t always agree with what’s written, and many times that’s exactly why I include it.
But at the very least, I can honestly say I read it to make sure it’s not complete trash before passing it on.
You would think that would be the standard in 2026, but here we are.
So the next time your favorite LinkedIn warrior shares an article with fifteen fire emojis and the phrase “So True!” take an extra minute before you hit repost. Open the article and read it.
If you want to read an actual article about the criminal use of AI: Dr. Ben Collier from the Center for Emerging Technology and Security at the Alan Turing Institute explores generative AI adoption in the criminal underground. https://cetas.turing.ac.uk/publications/cybercrime-vibercrime-assessing-generative-ai-adoption-criminal-underground
And sometimes…
That article posted to LinkedIn is gold! Steve Lenderman shared a link to a report on card fraud this week that turned out to be the best thing I’ve read in a while.
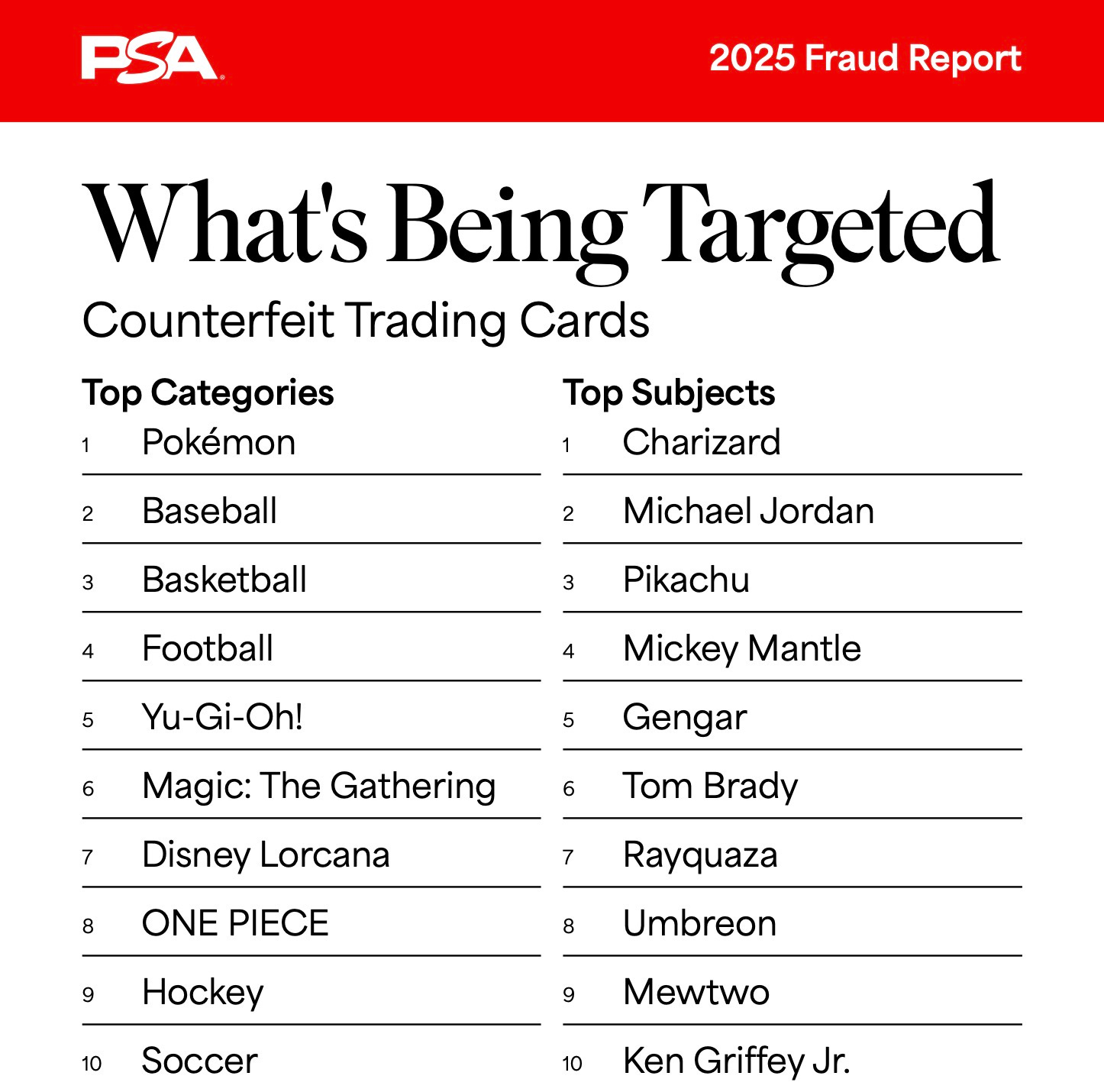
No, not that card fraud, the other card fraud. Counterfeit trading cards. Who knew an original Charizard was in such demand, or worth so much money???
The 2025 Card Fraud Report from collectible authentication company PSA is a must-read, if for nothing more than to broaden your view of the fraud landscape. For someone immersed in cyber fraud, the topic is fascinating. A whole different world.
The News
An investigation uncovered “Department 4’ at Russia’s Bauman Moscow State Technical University, which allegedly acts as a secret recruitment hub for the GRU, Russia’s military intelligence. Masked as an elite academic program, it trains students in advanced cyberwarfare skills such as password hacking, virus creation, and physical espionage, with the GRU controlling admissions, tests, and the placement of graduates into notorious hacking groups. The leaked 2,000 documents reveal that talented students are spotted as early as secondary school and assigned to units responsible for major cyberattacks worldwide. This is essentially a “hacker factory’. https://www.bitdefender.com/en-us/blog/hotforsecurity/inside-department-4-russias-secret-school-for-hackers
This makes me smile. Kids are beating age verification checks by wearing fake mustaches! https://www.theregister.com/security/2026/05/04/kids-can-bypass-some-age-checks-with-a-drawn-on-mustache/5224601
Securonix Threat Research has uncovered a phishing campaign that targets over 80 organizations primarily in the US by exploiting legitimate Remote Monitoring and Management (RMM) tools. The attack begins with impersonation emails mimicking the U.S. Social Security Administration, directing victims to compromised Mexican websites to download a malicious executable disguised as a government document. https://www.securonix.com/blog/venomous-helper-phishing-campaign/
You’re Invited! Psyche, how about some victimization instead? Fake invitations delivered via e-greeting cards are compromising accounts. https://tidbits.com/2026/05/11/beware-greeting-card-scams-from-trusted-senders/
And of course, Instructure, also known as Canvas, got hit, again. I won't spend time discussing it; a quick Google search can provide more details or the latest update on your school's likely recovery timeline.
Feedback
Send Feedback to matt(at)threatswithoutborders.com
dfir
Andrea Fortuna examines the challenges of cloud forensics, in which digital evidence is spread across multiple jurisdictions worldwide, forming a “jurisdictional labyrinth” that our traditional investigative techniques don’t easily navigate. Legal systems are increasingly in conflict, as seen in the conflict between the U.S. CLOUD Act, which claims jurisdiction based on the provider, even if data is stored elsewhere, and the EU’s GDPR, which limits cross-border data transfers unless there are specific international agreements. https://andreafortuna.org/2026/05/06/cloud-forensics-jurisdictional-labyrinth/
Cool Jobs
Fraud Manager, Everence Federal Credit Union. https://www.everence.com/about-everence/careers/current-positions/current-positions/2026/may/fraud-manager
Cool Tools
Has this image been edited? Use this to find out. https://imageedited.com/
Track flights from your desktop. https://flightradar.live/en/
Find a blog to follow. https://blogosphere.app/
Irrelevant
Joan Westenberg argues that the modern outrage cycle is intentionally crafted as a business strategy to generate engagement through provoked anger. She suggests that high-intensity anger is the most effective way to drive viral content, transforming digital platforms into “slot machines” that deliver outrage to keep users engaged and advertising revenue flowing. The best safeguard, she proposes, is **procedural emotional resistance**: resisting the algorithm's emotional pull by asking who gains from your reaction and remembering that your attention is the actual product being sold. https://www.joanwestenberg.com/outrag/
Sign Off
I attended several events around a college graduation this weekend and heard multiple speakers emphasize the importance of “your network”. There’s plenty of advice on how to build connections with co-workers, colleagues, and like-minded professionals. However, what seems to be missing from most advice is how to leverage that network effectively, how to make it work for you. Once you’ve built your network, what should you do with it? That’s the real nugget.
For example, a large and active network is useful if you’re unemployed. It’s easy to contact colleagues and post on social media, saying, “Hey everyone, I need a job.” But what if you’re already employed but low-key seeking a new opportunity? How do you leverage your network then? You can’t exactly broadcast that you’re looking for a new job, nor is it wise to post “open to work” on LinkedIn. Well, you could, but it would be best to submit your resignation to your current employer along with such a post. Is a large network really only an insurance policy in the event you become unemployed?
Thanks for reading another week. See you next Tuesday.
Matt
Published every Tuesday, Threats Without Borders offers original commentary and educational pieces related to cybercrime investigations and information security topics. We also summarize and comment on news articles concerning active threat intelligence for the financial industry. The newsletter interests everyone tasked with cybersecurity or involved in preventing or investigating technology-enabled fraud, theft, or money laundering.
Legal: I am not compensated by any entity for writing this newsletter. Obviously, anything written in this space is my own nonsensical opinions and doesn’t represent the official viewpoint of my employer or any associated organization. Blame me, not them.